What Is Secure Communications?
A Primer for Rights Defenders, Journalists, and Civil Society
Secure communications is the practice of communicating and sharing information using tools and protocols that prevent unauthorized access, interception, or monitoring by outside parties.
As more communication takes place online, ensuring secure and private digital communications has become increasingly important for civil society organizations, journalists, and human rights defenders. This is because these groups, due to the nature of their work, often handle sensitive information that could lead to serious risks or harm if it falls into the wrong hands. In order to maintain secure communications, two central things are usually required:
Secure communication technologies and infrastructure
A culture of security where specific habits and practices are fomented and in place.
In this primer, we provide an overview of the technologies, but mostly focus on guidance around how to foment security culture, which is the most important starting point.
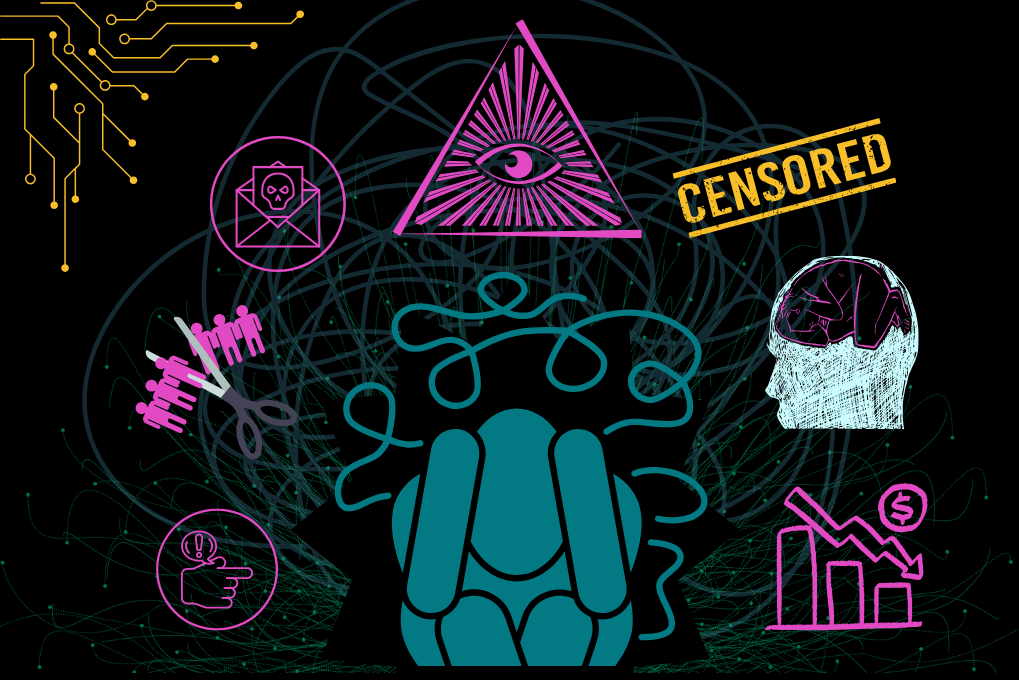
Why Secure Communications Matters
The following are examples of situations in which maintaining secure communications are especially important:
A journalist communicating with a whistleblower to both discuss issues and share documents.
A civil society organization’s HR department exchanging information with an employee, including home address, bank details, etc.
A grassroots group coordinating actions in a highly restrictive, oppressive environment.
A human rights event arranging travel for an individual with a high-risk profile.
A network of CSOs forming a coalition against a specific abuse, requiring them to share strategies, tactics, contacts, and other sensitive information required to coordinate.
A CSO working on a legal case against a government or big company discussion the litigation strategy with legal counselors, witnesses, or other sensitive actors.
In these situations, unauthorized access to sensitive information could have serious consequences, including legal risks, harassment, intimidation, or even physical harm.
What Are Secure Communication Technologies and Infrastructure?
Secure communication technologies and infrastructure refer to the tools, systems, and technical configurations used to protect the confidentiality, integrity, availability, and privacy of information or communications shared between individuals or groups. They help prevent unauthorized access, interception, surveillance, or tampering with communications.
Setting Up Secure Communications
The technology setup appropriate for your network to communicate and share information will depend on factors such as the number of users, the sensitivity of the information involved, your threat model, and available resources. Because these decisions can be complex, it is best to consult individuals in your network with relevant technical expertise. If your group does not have this expertise, consider reaching out to trusted neighbors, family, or friends, who may have this expertise, for guidance.
Examples of Secure Communication Technologies
Examples of secure communication technologies include encrypted messaging applications, secure email services, virtual private networks (VPNs), and tools that support end-to-end encryption. Infrastructure refers to the underlying technical environment that enables secure communication, such as properly configured devices, secure servers, strong authentication methods, and even tools like TLS/HTTPS.
Secure communication technologies and infrastructure help reduce digital risks by ensuring that sensitive information is transmitted and stored in ways that make unauthorized access more difficult. However, it's important to note these technologies
are not bulletproof, but their effectiveness can be strengthened if the network of users are fomenting good security practices and culture (more on this below).
Secure Communications: The Practices
While open-source tools and properly configured technical infrastructure can provide important encryption, security, and privacy benefits, secure communications ultimately begins with the everyday habits and practices we adopt in our community, group, or organization.
Secure communications is not only about the technology we use, but also about the culture of security we foment collectively — often supported through shared policies, guidelines, and agreed-upon practices. Since communication involves more than one person, this means that the security depends on the actions of everyone involved. This is precisely why you will often hear security specialists state that a network is only as secure as its weakest link.
As an example, imagine a group of six people where five members consistently follow agreed-upon protocols, processes, and tools. If the sixth person shares sensitive information on an insecure platform or through unprotected channels, the privacy and security of the entire group is compromised.
This is why, in many cases, cultivating security awareness can be more important than the actual technology used. Below are some tips collected from TCU’s community members.
🍃 Decide What Not to Discuss or Share Online
In some situations, the safest approach is to avoid discussing certain topics digitally or on specific platforms or online spaces.
For example, a network may decide that lists of community members should never be shared through email, but only through trusted encrypted tools. Some networks may determine that certain conversations can take place on platforms like Signal because it's encrypted, open source, and part of the digital rights ecosystem, but not on Meta-owned Whatsapp. Establishing clear boundaries around what should and should not be shared digitally helps reduce the risk of unintended exposure.
At the same time, it is important to strike a balance. Members still need to communicate in order to coordinate, organize, and work effectively. Encouraging network members to think critically about how much information is truly necessary before sharing can help reduce oversharing of sensitive details. This is part of practicing data minimization, which reduces the potential impact if communications are compromised.
It is also helpful for individuals to consistently consider the potential impact of the information they are sharing. For example, asking how could specific details be used if accessed by adversaries? Encouraging members to reflect on how, why, and what they are sharing can help them make more informed decisions. As an example, members of a network may agree to discuss agenda items digitally, but only share the physical location of an in-person meeting verbally.
🍃 Set Time Limits for Messages and Data When Possible
Many communication apps allow users to set disappearing messages that are automatically deleted after a specified period of time. This feature can help reduce the amount of sensitive information stored long-term on devices or servers. Additionally, administrators can use data retention policies to ensure that specific types of data are deleted after a certain period of time. As an example, deleting registration lists from events that are older than three years.
Threat environments can change over time, and information that feels safe to share today may become more sensitive in the future. Setting time limits on messages, and having data retention policies, can reduce the likelihood that older conversations or unnecessary historical data remain accessible and a point of vulnerability.
🍃 Verify Individuals Before Adding Them to Online Spaces
Even the most secure technical tools cannot protect your network if untrustworthy individuals are added to shared online spaces. Before adding someone to a virtual community space, such as a chat or shared folder, it is good practice to verify their identity and confirm their trustworthiness with others. As an example, imagine your network decides to create a chat group on Signal to mobilize different partners. The community manager or administrator of the group may ask that existing and trusted members of the chat vouch for the person before they are added to the shared space. Taking time to verify individuals can help reduce exposure of sensitive information and strengthen the overall security of shared spaces where either communications or data is shared.
However, verification processes cannot guarantee complete safety. Movements and organizations have to constantly manage potential infiltration attempts by adversaries.
In a recent case, the FBI gained access to a private Signal group chat of immigrants’ rights activists who were organizing “courtwatch” efforts in New York City. While how the infiltration happened is still under investigation, many digital rights experts believe that someone was added to the group that was working with the FBI. Notably, the more people are added to an online shared space, the more difficult it is to ensure security. For these reasons, we recommend that for online spaces that are larger than say 5 to 10 people, members are recommended to treat those spaces like public spaces in regards to what they share, even if those spaces are private or invite-only. Encouraging a false sense of security is one of the worst things administrators and community managers can do.
🍃 Balance Usability and Security
Even the most secure technologies cannot protect your network if they are too difficult or inconvenient to use consistently. Choosing tools that people understand and are willing to use regularly helps ensure that secure communication practices are applied consistently across the network.
It is also common to see security advice nudging networks towards tools that require data bandwidth or storage that some members' devices lack, making the advice not only counterproductive in terms of usability and adoption but also exclusionary for people without the resources needed to effectively sustain the security practice. (More on other challenges around security communications implementation below.)
When selecting tools or designing protocols, it can be helpful to start by understanding how people are already communicating. Building strategies around existing habits increases the likelihood that safer practices will be adopted successfully. For example, if members primarily use mobile devices rather than desktop computers, selecting tools that work well on mobile may be more effective than introducing solutions that require unfamiliar workflows.
🍃 Cultivate a Culture of Security and Support Less Technical Members
Offer training and support to members who may have less technical experience. Helping everyone understand your communication tools, policies, and workflows strengthens overall security while building shared knowledge across the group.
Cultivating a strong security culture also means encouraging questions and making it clear that no question is unimportant. Individuals should feel comfortable acknowledging when they do not understand something or need additional guidance. An environment that supports learning helps prevent mistakes and strengthens collective security practices.
Some communities have also found success introducing new tools through collaborative or social learning environments, such as group workshops or informal meetups where members can experiment with technologies together.
🍃 Normalize Enforcing Security Boundaries
Group administrators and community managers should be prepared to take action when behavior puts the safety or security of the network at risk. Clearly communicating expectations about acceptable practices is essential. These expectations may be documented through security policies, community guidelines, or codes of conduct.
It is also important to normalize protective actions such as removing participants from group chats or restricting access to sensitive information when security practices are not followed. While enforcing boundaries may feel uncomfortable, doing so is often necessary to protect the trust, privacy, and safety of the broader network.
Challenges of Secure Communications
Ensuring secure communications can be complicated, presenting a range of challenges for both organizations and communities. These challenges vary depending on the threats a specific network faces, the sophistication of potential adversaries, the financial or technical resources available to them, and the actual size and needs of the network.
For example, a grassroots organization with thousands of volunteers may lack the resources to hire dedicated technical staff to build and maintain the infrastructure it needs for secure communications. By contrast, a grassroots group of five people would not require the same level of infrastructure. Similarly, a large human rights organization operating across multiple regions faces varied risk environments and may be targeted by numerous well-resourced, government-backed adversaries, and may have a harder time enforcing a culture of security across its multiple employees. In contrast, a small domestic violence shelter serving a local community is likely to face fewer vulnerabilities, threats, and risks, with the smaller staff being able to more effectively enforce a stronger culture of security if it were needed.
Information Overload
One commonly reported challenge is the growing number of communication platforms, group chats, channels, and servers that people must manage simultaneously. This can create information overload, making it more difficult to keep track of important discussions and increase the likelihood that sensitive information is shared in the wrong place or with unintended audiences.
Limited Resources andTechnical Know-How
Many networks also struggle with deciding which tools to trust as they try to navigate off of big tech solutions, which while many times “free,” collect user data or change policies over time. Limited access to technical knowledge, security expertise, or financial resources can further complicate decision-making. Even when more secure options exist, networks often face questions about long-term sustainability, trust, accessibility, and whether tools will remain aligned with privacy and security values in the future.
For example, a group of activists may seek to move away from widely used platforms such as WhatsApp or Google Docs, but lack the resources needed to host or maintain more privacy-preserving, open-source alternatives. Even when open-source solutions are adopted, questions may arise about long-term sustainability, as some projects depend on limited funding or volunteer contributions to ensure continued maintenance and security.
Secure Communications Educational Resources
The following is a list of favorite resources our community members have shared. This will be updated as we receive new recommendations.
Locking down Signal - Freedom of the Press Foundation
Communicating With Others - Surveillance Self-Defense from the Electronic Frontier Foundation
Easy, short, and introduces a-bit-more-complex subjects. Full of links if people want to know more.
How HTTPS and Tor Work Together to Protect Your Anonymity and Privacy - Surveillance Self-Defense from the Electronic Frontier Foundation
A community organizer’s guide to Signal group chats - The Verge
https://securemessagingapps.com - Secure Messaging App Comparison Site
Shira Quiz from Horizontal, developers of Shira App
An educational and very practical resource to avoid phishing and communicate securely.
Using Signal groups for activism - Micah Lee